Following on from my earlier posts: -
SSL configuration:
Default server
Server name: bpm856.uk.ibm.com:8080
SSL enabled: NO
SSL server defined at: /opt/IBM/HTTPServer/conf/httpd.conf:852
Server name: bpm856.uk.ibm.com:8443
SSL enabled: YES
FIPS enabled: 0
Keyfile: /opt/IBM/HTTPServer/ssl/keystore.kdb
Protocols enabled: TLSv10,TLSv11,TLSv12
Ciphers for SSLV2: (protocol disabled)
Ciphers for SSLV3: (protocol disabled)
Ciphers for TLSv10: (defaults) TLS_RSA_WITH_AES_128_CBC_SHA(2F),TLS_RSA_WITH_AES_256_CBC_SHA(35b),SSL_RSA_WITH_3DES_EDE_CBC_SHA(3A)
Ciphers for TLSv11: (defaults) TLS_RSA_WITH_AES_128_CBC_SHA(2F),TLS_RSA_WITH_AES_256_CBC_SHA(35b),SSL_RSA_WITH_3DES_EDE_CBC_SHA(3A)
Ciphers for TLSv12: (defaults) TLS_RSA_WITH_AES_128_GCM_SHA256(9C),TLS_RSA_WITH_AES_256_GCM_SHA384(9D),TLS_RSA_WITH_AES_128_CBC_SHA256(3C),TLS_RSA_WITH_AES_256_CBC_SHA256(3D),TLS_RSA_WITH_AES_128_CBC_SHA(2F),TLS_RSA_WITH_AES_256_CBC_SHA(35b),SSL_RSA_WITH_3DES_EDE_CBC_SHA(3A)
Syntax OK
Save the Configuration
I've made yet more headway with this fascinating product.
I'd referenced this excellent post: -
which, in part, included the necessary F5 commands, using the tmsh utility, to set up a pair of network interfaces, some IP addresses and a default route: -
<snip>
tmsh create net vlan external interfaces add { 1.1 { untagged } }
tmsh create net vlan internal interfaces add { 1.2 { untagged } }
tmsh create net self 10.128.10.240 address 10.128.10.240/24 vlan external
tmsh create net self 10.128.20.240 address 10.128.20.240/24 vlan internal
tmsh create net route Default_Gateway network 0.0.0.0/0 gw 10.128.10.2
tmsh save sys config
</snip>
However, I wanted to go further - I wanted to script the configuration of the necessary components: -
HTTPS Health Monitor
Node
Virtual Server
to allow the F5 to do its job of (a) monitoring a downstream instance of IBM HTTP Server and (b) allow me to have IHS listening on port 8443 whilst the F5 receives traffic on port 443.
This is my IHS configuration, for the record: -
/opt/IBM/HTTPServer/bin/apachectl -DDUMP_SSL_CONFIG -f /opt/IBM/HTTPServer/conf/httpd.conf
SSL configuration:
Default server
Server name: bpm856.uk.ibm.com:8080
SSL enabled: NO
SSL server defined at: /opt/IBM/HTTPServer/conf/httpd.conf:852
Server name: bpm856.uk.ibm.com:8443
SSL enabled: YES
FIPS enabled: 0
Keyfile: /opt/IBM/HTTPServer/ssl/keystore.kdb
Protocols enabled: TLSv10,TLSv11,TLSv12
Ciphers for SSLV2: (protocol disabled)
Ciphers for SSLV3: (protocol disabled)
Ciphers for TLSv10: (defaults) TLS_RSA_WITH_AES_128_CBC_SHA(2F),TLS_RSA_WITH_AES_256_CBC_SHA(35b),SSL_RSA_WITH_3DES_EDE_CBC_SHA(3A)
Ciphers for TLSv11: (defaults) TLS_RSA_WITH_AES_128_CBC_SHA(2F),TLS_RSA_WITH_AES_256_CBC_SHA(35b),SSL_RSA_WITH_3DES_EDE_CBC_SHA(3A)
Ciphers for TLSv12: (defaults) TLS_RSA_WITH_AES_128_GCM_SHA256(9C),TLS_RSA_WITH_AES_256_GCM_SHA384(9D),TLS_RSA_WITH_AES_128_CBC_SHA256(3C),TLS_RSA_WITH_AES_256_CBC_SHA256(3D),TLS_RSA_WITH_AES_128_CBC_SHA(2F),TLS_RSA_WITH_AES_256_CBC_SHA(35b),SSL_RSA_WITH_3DES_EDE_CBC_SHA(3A)
Syntax OK
and this is what I did on the F5 LTM: -
Create a HTTPS Monitor
This is the component that monitors the downstream IHS, so needs to "know" the HTTPS ciphers being used and the port. Note that, in Unix-land, port 8443 is "known" as pcsync-https ( just check /etc/services ) which is an alias for port 8443.
The Monitor also needs to send a well-formed HTTP/1.1 request, and wait for a proper HTTP response code e.g. 200 OK.
tmsh create ltm monitor https davehttps { cipherlist DEFAULT:+SHA:+3DES:+kEDH compatibility enabled defaults-from https destination *:pcsync-https interval 5 recv 200 send "GET /index.html HTTP/1.1\\r\\nHost: bpm856.uk.ibm.com\\r\\nConnection: Close\\r\\n\\r\\n" time-until-up 0 timeout 16 }
Create a Node
The node ( we typically have more than one ) refers to the downstream IHS box, specifically in terms of it's IP address or hostname
Create a Pool
This is where the Monitor and the Node are brought together
tmsh create ltm pool bpm856.uk.ibm.com_ihs members add { bpm856.uk.ibm.com:pcsync-https { monitor davehttps }}
Create a Virtual Server
This represents the service that the LTM offers to the client, which is where the magic "mapping" between the IHS port of 8443 and the exposed port of 443 happens
tmsh create ltm virtual IHS destination 10.128.10.240:https ip-protocol tcp mask 255.255.255.255 pool bpm856.uk.ibm.com_ihs profiles add { clientssl { context clientside } http{} serverssl{context serverside } tcp{} } source 0.0.0.0/0 source-address-translation { type automap } vlans add { external internal } clans-enabled
Save the Configuration
I think this is implicit, but it never hurts to do it :-)
tmsh save sys config
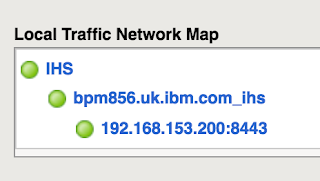
Having run all of that, which takes about 5 seconds, I have a nice network map: -
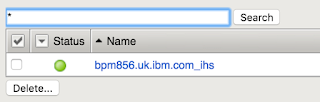
an active pool: -
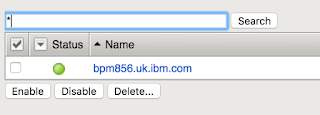
a working node: -
and a happy virtual server: -
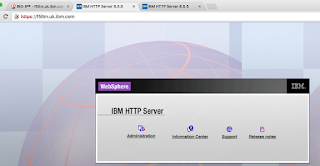
More importantly, I can hit IHS directly: -
*AND* via the LTM: -
Note that, in the latter case, the connection is on port 443, which the browser automatically hides :-)
So I've still got some SSL certificate stuff to do, especially if I want to have the F5 use Mutual Authentication ( aka Client Authentication ) to the IHS box, but that's for another day ….